This
article is on overview about the functions and scenarios using PowerShell in
the context of Azure Information Protection. Everything in this article is
based on the official Microsoft documentation.
Microsoft published a
brilliant Admin Guide about using PowerShell with Azure Information Protection containing
all details and scenarios: Admin Guide: Using PowerShell with the Azure Information
Protection client.
Overview
In Azure
Information Protection we can use PowerShell to:
- Administering Azure Information Protection
- Configuration for the super user feature
- Using Azure Information Protection
- Work with the AIP Scanner
Azure
Information Protection knows two PowerShell modules.
- AADRM: These cmdlets are used to administer the protection service (Azure Rights Management) for Azure Information Protection.
- AzureInformationProtection: These cmdlets are used to protect files, label files, and get information about files.
First step
is to install the AADRM PowerShell module. To do this open PowerShell and use: Install-Module
-Name AADRM. For more details and requirements
about how to install AADRM PowerShell modules read this article: Installing
the AADRM PowerShell module
To get an
overview of all cmdlets use: Get-Command -Module AADRM or look at this list: Cmdlets
grouped by administration task
The AzureInformationProtection
cmdlets are part of the Azure Information Protection client. These cmdlets can
be used with Azure Information Protection, the protection service (Azure Rights
Management), and Active Directory Rights Management Services (AD RMS).
To get an
overview of all cmdlets use: Get-Command -Module AzureInformationProtection
Main scenarios and some examples
We can use PowerShell
for AIP for classification and protection. Let’s have a deeper look on some
typical scenarios:
Scenario 1: remove protection from files for others using your own account
In this
scenario we need PowerShell to configure the “super user feature”. In addition,
we need to configure your account to be a super user for Azure Rights
Management. To enable the super user feature, use the PowerShell cmdlet Enable-AadrmSuperUserFeature To assign your user or a groups we can use the Add-AadrmSuperUser cmdlet.
To get a complete
overview about the super user
feature in AIP refer to this official article: Configuring
super users for Azure Rights Management and discovery services or data recovery
The super user feature is also needed if we
need to index mailboxes for search operations or if DLP solutions. CEG or
anti-malware products can also use the super user to inspect files that are protected
by AIP.
Scenario 2: protect or unprotect files without user interaction
First step
in this scenario is to connect to Azure Rights Management Service by using this
cmdlet: Connect-AadrmService. To login enter
your Azure Information Protection tenant administrator credentials.
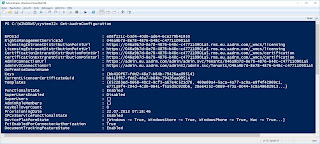
To get an overview
about the ARM instants and to verify that the login was successful use: Get-AadrmConfiguration. The result will be something like this for example:
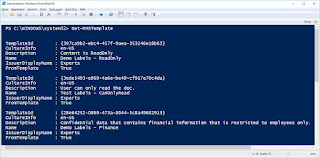
In the next step we will use PowerShell to get a
list of all available Labels using this cmdlet: Get-RMSTemplate.
In my example it looks like this:
Now we can to several
things:
- Protect a file: Protect-RMSFile -File C:\Test.docx -InPlace -TemplateId e6ee3481-26b9-45g5-b33a-f774escd43b0
- Protect all files in a folder: Protect-RMSFile -Folder \ServerABC\Docs -InPlace -TemplateId e6ee3481-26b9-45g5-b33a-f774escd43b0
- Get the status of a file: Get-RMSFileStatus -File \Server1\Documents\TestABC.docx
- Remove protection: Unprotect-RMSFile C:\testDoc1.docx -InPlace
Related
posts:
- Azure Information Protection Part I – Overview
- Azure Information Protection Part III – AIP Scanner
- AzureInformation Protection Part IV – Work with AIP
- Azure Information Protection Part V – Advanced features
Keine Kommentare:
Kommentar veröffentlichen