Microsoft
finally release the Compliance Manager: https://servicetrust.microsoft.com/ComplianceManager
This
framework is designed to help companies getting and staying GDPR compliant or
do other audits like ISO 27001:2013.
This
article is focusing on GDPR topics.
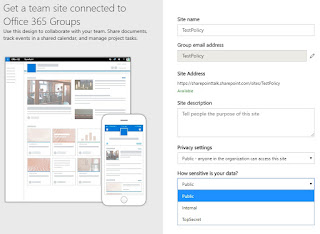
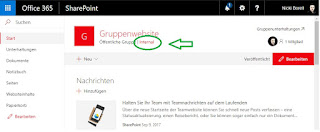
Services included in this cloud service assessment
SharePoint
Online, Exchange Online, Microsoft Booking, Microsoft Graph API, Microsoft
Analytics, Microsoft Planner, Microsoft Stream, Office Delve, Office 365 Groups,
Office 365 Video, Sway, Microsoft StaffHub, Microsoft PowerApps, Microsoft
Teams, Skype for Business
Microsoft Managed Controls
Article 4
Number 8 of the GDPR defines that an entity that processes data on behalf of
another is considered to be a contract data processor. Therefore Microsoft,
with its services Office 365 & Azure is clearly a contract data processor
within the meaning of Article 4 Number 8 of the GDPR.
Because of
this there are also topics that Microsoft has to fulfill and the contracting
entity had to check. These topics are aggregated in the “Microsoft Managed
Controls” section of Compliance Manager.
The topics
in this section are passed and tested by a third party independent auditor. We
can get the details about every topic in the Compliance Manager as you can see
in this example:
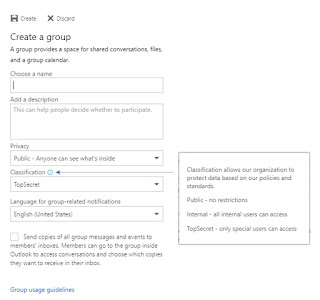
Customer Managed Controls
Not every GDPR
article is about IT systems. Because of this not every article is covered by the
Compliance Manager framework. In the section “Customer
Managed Controls” Microsoft offers an audit tool that can be used to organize
you GDPR compliance journey for Office 365 & Azure.
Features to organize GDPR compliance journey
- Assessment a topic to a responsible person
- Upload and manage documents
- Track status
- Test date
- Track test result
- Detailed description for each topic
- Documentation about your implementation details
- Documentation about your test plan & management response
Example:
You can use
the Compliance Manager framework web UI to work with an auditor or you can also
export the results as an Excel files.
Mapping
The GDPR is
structured by the following topics:
- General provisions (Article 1 - 4)
- Principles (Article 5 - 11)
- Rights of the data subject (Article 12 - 23)
- Controller and processor (Article 24 -43)
- Transfers of personal data to third countries or international organisations (Article 44 - 50)
- Independent supervisory authorities (Article 51 - 59)
- Cooperation and consistency (Article 60 - 76)
- Remedies, liability and penalties (Article 77 - 84)
- Provisions relating to specific processing situations (Article 85 - 91)
- Delegated acts and implementing acts (Article 92 - 93)
- Final provisions (Article 94 - 99)
Microsoft
as a Software company is using different topics:
- Discover
- Manage
- Protect
- Report
Even the Compliance
Manager framework is using a different structure. The framework is separated in:
- Office 365 in-Scope Cloud Services (List of covered services)
- Microsoft Managed Controls (Topics Microsoft has to fulfill)
- Customer Managed Controls (Topics the customer has to fulfill)
So we need
to do a mapping.
The
following matrix is showing the chapters, the articles and the subitems covered
by Compliance Manager framework. You can use this in you company-wider GDPR
audit to get a clear overview of what is relevant in the context of Office 365
& Azure and what is covered by the Microsoft Compliance Manager framework.
File can be
downloaded here -> LINK
Remarks:
Not every
article need to be fulfilled by every company. In detail it depends on your
company structure and what you do in detail with personal data. A general
evaluation of which of these articles apply in a specific individual case, must
be analyzed in a legally robust manner.
This article
and the Excel Matrix was created to the best of the author’s knowledge and
according to careful research. However it cannot and does not intend to replace
an in-depth legal, process, and technical assessment.
Related articles: GDPR/DSGVO Field Guide for Office 365 & Azure